
by Ciright | Jan 23, 2026 | Blogs
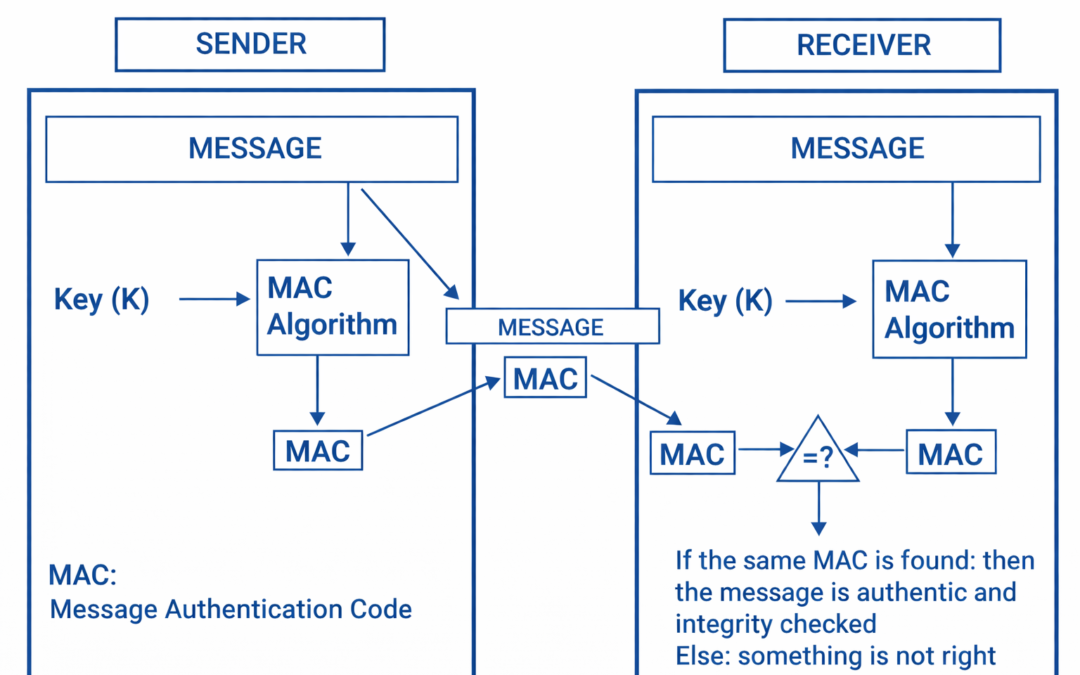
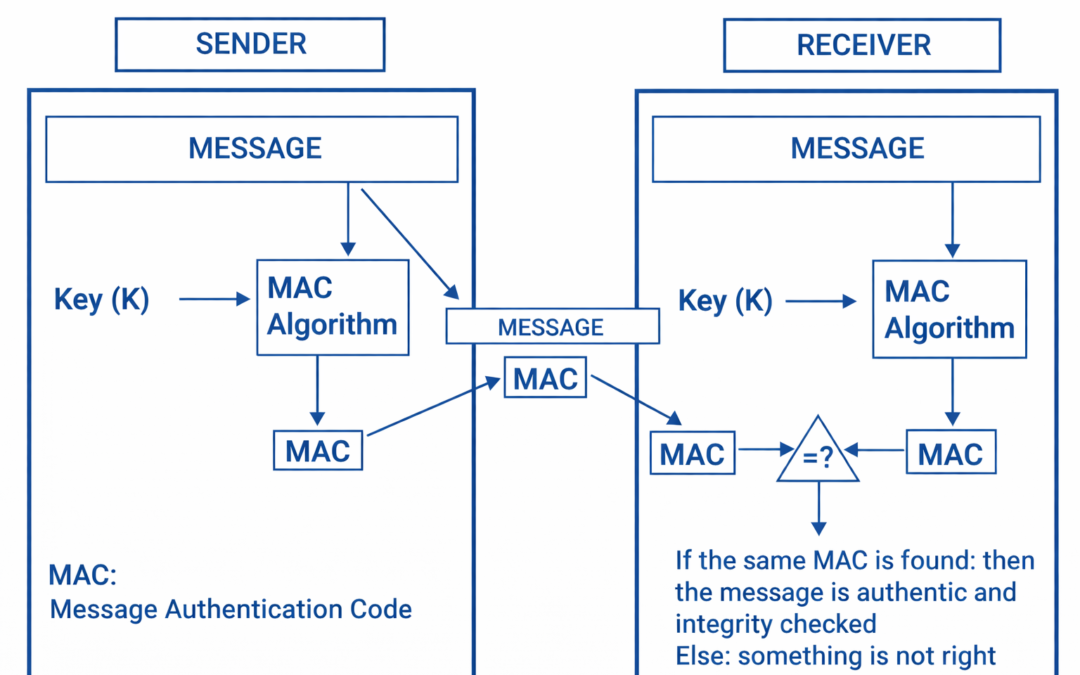
Dear Readers, Message Authentication Code (MAC), also referred to as a tag, is used to authenticate the origin and nature of a message. MACs use authentication cryptography to verify the legitimacy of data sent through a network or transferred from one person to...

by Ciright | Jan 23, 2026 | Blogs
Dear Readers, MIFARE® is NXP’s well-known brand for a wide range of contactless IC products with a typical read/write distance of 10 cm (4 inches) used in more than 40 different applications worldwide. With more than 12 billion contactless and dual interface IC’s...

by Ciright | Jan 23, 2026 | Blogs
Dear Readers, Mobile credit card swiper – UNIIMAG II (Android) Equipped with the most secure encryption key available on the market, the UNIIMAG II mobile credit card reader keeps your data safe while allowing you to accept payments on the go. Order your Mindbody...

by Ciright | Jan 23, 2026 | Blogs
Dear Reader, Equipped with the most secure encryption key available on the market, the UNIIMAG II mobile credit card reader keeps your data safe while allowing you to accept payments on the go. Order your Mindbody mobile credit card reader here! Contents Requirements...

by Ciright | Jan 23, 2026 | Blogs
Dear Readers, What is NFC Card Emulation Mode? An NFC enabled device can operate in three different modes – reader/writer mode, peer-to-peer mode and the all important card-emulation mode. In Reader/Writer mode, an NFC...


Recent Comments