Tech Talk
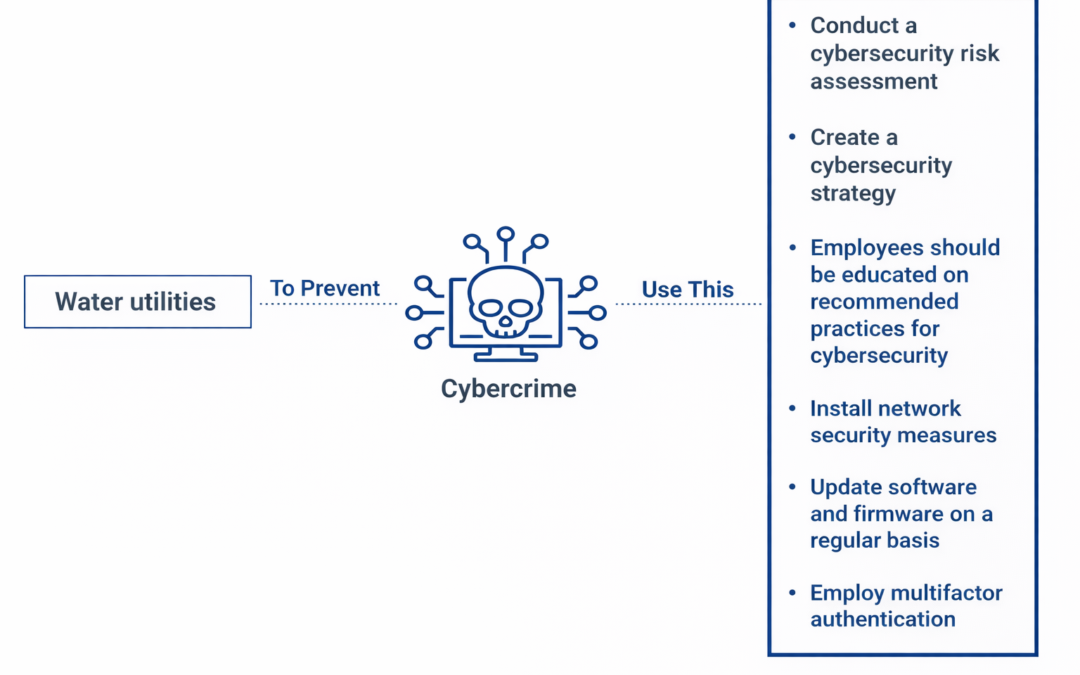
How can water utilities be protected against cybercrime?
Dear Readers,
Water utilities are vital community services that supply safe drinking water and wastewater treatment. They are, nevertheless, vulnerable to cybercrime, just like any other essential infrastructure. Hackers might compromise the water utility’s network and produce a variety of negative consequences, including as manipulating the water supply, interrupting operations, or stealing critical data. As a result, safeguarding water utilities from cyber attacks is critical to ensuring public safety and the integrity of the water supply.
Water utilities can take the following steps to protect themselves from cybercrime:
Conduct a cybersecurity risk assessment: A risk assessment is a critical step in detecting potential weaknesses and threats to the water company’s security. The review should include identifying essential assets, potential vulnerabilities, and potential threats. This will help determine the best security policies and activities to take to mitigate the dangers.
Create a cybersecurity strategy: After the possible risks have been identified, it is critical to create a complete cybersecurity plan that includes policies, processes, and technical controls to protect against cyber attacks. This strategy should address issues such as access control, data security, and incident response.
Employees should be educated on recommended practices for cybersecurity: Workers are frequently the weakest link in any cybersecurity strategy. As a result, it is critical to teach personnel on appropriate procedures for recognizing and reporting possible cyber risks. This includes phishing assaults, social engineering, and other cybercriminal strategies.
Install network security measures: To monitor network activity and detect suspicious behavior, water utilities should adopt network security measures such as firewalls, intrusion detection and prevention systems, and security information and event management (SIEM) solutions.
Update software and firmware on a regular basis: Updating software and firmware on a regular basis is critical for preserving the network’s security. These updates frequently include essential security fixes that fix known vulnerabilities.
Employ multifactor authentication (MFA): MFA adds an extra degree of security to prevent illegal access. Before entering the network, users must give two or more authentication elements, such as a password and a fingerprint.
Ciright Integrates Pen Mail into an AS400 platform
Pen Mail, which is a pen-based email notification that connects to the ATT easy link service. It is built to integrate into an AS400 platform and many other main frame mail systems to provide mobility to the professional and mobile work force for electronic mail.
Ciright Debuts with While You Were Out Application on Casio Zoomer
Ciright developed the WYWO Application that was formatted on Casio Zoomer product where the WYWO message could be captured in the office and disseminated through various networks, primarily the paging network, to send a 256 character message that was then parsed and...
RailSpec Increases the Safety and Integrity of the Northeast Corridor
Ciright is proud to introduce RailSpec, a comprehensive program for the field workforce of the railroad industry designed to run on the Norand PenKey 6100. While walking and inspecting tracks, workers are now able to simultaneously report and detail work orders for...
Ciright Announces Solution for Patient Assesment in Private Practices and Hospitals
Ciright announces the Patient Assessment App on the PT 9000 which allows a nurse or a physician to do a comprehensive patient assessment including medical history, family history, allergies, in addition to other criteria that are assessed when a patient enters a...
Ciright Unveils Field Batch Data Capturing System
Ciright develops Field Batch Data Capture System, which is a tool used to acquire surveyed information across multiple industries that can then be batched loaded through a san disc card in which the access to wireless network is either cost prohibited or there is not...
Ciright Develops Pen-Based Application for Prescription Management
Ciright developed Fax RX which was an integrated, pen-based application for a doctor to write a prescription and fax it to a pharmacy. The product was developed in PenRight to run on a Sharp PT 9000 running a GeoWorks Operating System, where PenRight was overlay on...

Recent Comments