Tech Talk
Multi-factor Authentication in Government Sector
Dear Readers,
This week’s blog is about Multi-factor Authentication in Government Sector; Cyberattacks continue to be a major concern for the state and local government sector, local officials, city councils, and other government entities. It is predicted that such cyberattacks will continue to rise. So, what makes the government sector so appealing to attackers? Let’s find out.
Ambimat Electronics, with its experience of over forty years, desires to draw the attention of its readers and potential customers towards this blog post about their new product called AmbiSecure key and how it will benefit us.
Multi-factor Authentication in Government Sector
Cyberattacks continue to be a major concern for the state and local government sector, local officials, city councils, and other government entities. It is predicted that such cyberattacks will continue to rise. So, what makes the government sector so appealing to attackers? Let’s find out.
Why Government Sectors are being targeted?
The amount of information stored by government agencies is immense. Most of them are classified data concerning their citizens. Massive disruption can occur if this data is compromised. It can even stop the services that many of us depend on. Additionally, government sector employees are working constantly round the clock. In such a situation, they can easily be distracted and fall prey to phishing attempts. Cybersecurity readiness is still lacking in most government sectors, as there are not enough IT professionals equipped with the knowledge to implement a high level of security. There is also an absence of awareness in regards to cyber threats across many government sectors.
It is surprising that even with a significant rise in cyberattacks in the government sector, many officials are still hesitant in implementing cybersecurity measures to address them. What is more shocking, is that they are unaware of the fact of how often they are being targeted. These are some of the issues for the government sector to become a victim of cyberattacks and threats.
Defining Cyber Threats
Cyber attackers are not lenient on those who are unprepared, especially in the government sector. Apart from developing newer threats, that IT departments are unaware of, cyber attackers also rely on using the old ways of phishing and ransomware, as such methods have still proven to be effective and successful. Moreover, they are easy to launch. Needless to say, an overworked employee is likely to cause an error, and threats actors are always ready to abuse these errors. One simple error of logging into an illegitimate phishing website can result in huge financial losses and damages for the government.
Some of the newer and harsher means of cyber-attacks that the government sector is likely to face, and is unsure how to protect themselves against it, are MFA-resistant phishing attacks.
Threat actors continuously work around the clock to break protection barriers, and over the years they have managed to dodge Multi-Factor Authentication protections such as SMS and OTPs authentication methods, which can now be intercepted by attackers.
Cyberattacks in the government sector are not limited to just phishing and ransomware, it extends to election meddling and manipulation. Not only hackers but foreign governments have been accused of prying into government election campaigns to create fear, uncertainty, and doubt in the results. Therefore, it can be rightly said that government entities are vulnerable from all sides, and threats can come in different forms and target different areas. As long the threats exist, the fight to stop them will continue for the government sector.
Improve Cybersecurity Readiness
Overall security cannot be achieved overnight. However, by implementing cybersecurity readiness government entities can improve their security.
Minimizing the Attack Surface
In a remote work environment, minimizing the attack surface has become a difficult task. However, by distinguishing the areas by which a cyber attacker can get access to systems and resources, the government sector can apply appropriate security to it. Today, many government organizations are shifting towards a zero-trust architecture to minimize the attack surface. A no trust, always verifies policy can significantly reduce the attack surface, as all access is provided after verification.
Training
Training is an essential element when dealing with cybersecurity matters. Giving the necessary education to employees regarding the present and future threats will reduce man-made mistakes significantly. The government sector should invest in strong cyber awareness programs that teach staff about phishing attacks, ransomware, man-in-the-middle attacks, malware, etc. Such programs will lower the number of stolen credentials and overall attacks. A strong email filtering system will also help reduce the threat arising from phishing emails.
Strong MFA Solution
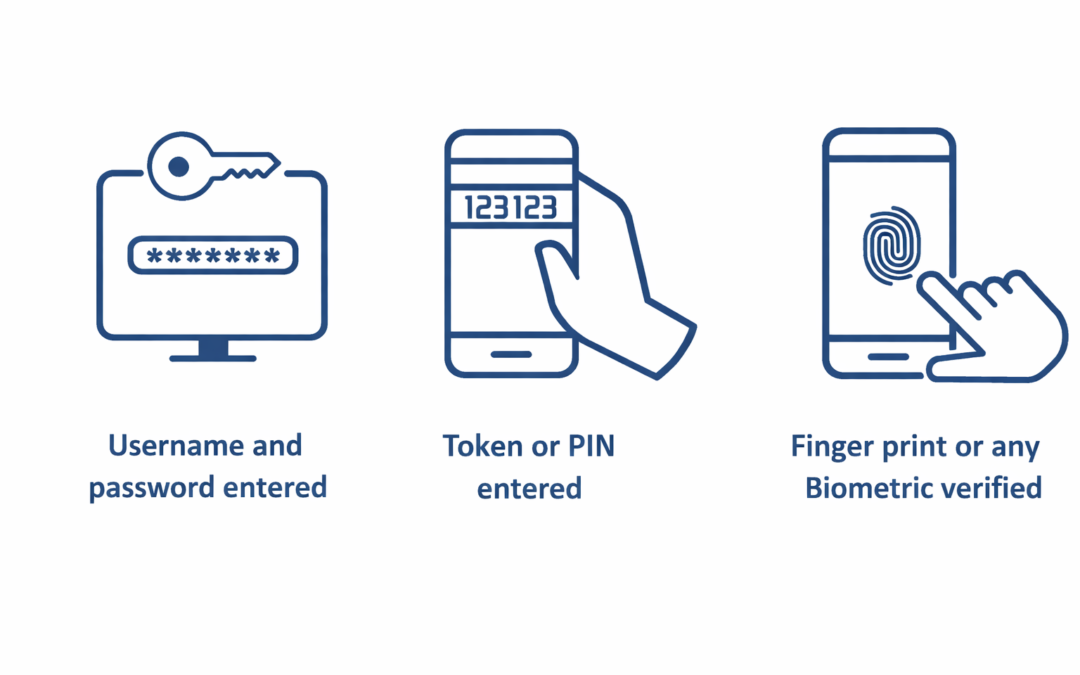
Even with MFA-resistant phishing which targets SMS and OTPs, government organizations can still implement strong multi-factor authentication methods. These methods can include the use of biometrics which cannot be easily compromised. Apart from this, the use of hardware security keys and card will also protect user accounts from breaches. Such a type of authentication mechanism can prevent cyberattacks from happening in the government sector.
Cyber threats will continue to haunt government organizations from every direction. They will not go away anytime soon. However, by being vigilant and ready government entities can prevent cybersecurity threats.
Reference:
Improve Government Security with AmbiSecure
FIDO2 is a standard that simplifies and secures user authentication. It uses public-key cryptography to protect from phishing attacks and is the only phishing-proof factor available. Government Organizations around the world and across many sectors, including healthcare, can benefit from Fast Identity Online or Fast ID Online (FIDO) authentication, which their employees and users can use to minimize security risks and improve overall user experience. The AmbiSecure key and card are FIDO certified which offers superior security by combining hardware-based authentication and public key cryptography to effectively defend against phishing attacks and eliminate account takeovers.
Twitter Support for WYWO Arrives!
Ciright is thrilled to join the thousands of services that support one of the newest, fastest growing social networks on the internet. Tweet and retweet all from your WYWO app, insuring you never miss a message again.
Ciright Introduces Professional Services Business Automation Application
Today, Ciright announced the availability of the Professional Services Business Automation Application providing visibility and accountability of all activity prior to professional service contract occurring. The system integrates the cost per employee by the sales...
Ciright Focus on Capital Goods
Ciright announces availability of the Capital Goods focus. This fully integrated application supports both manufacturers and channels needs to enhance the sales of capital goods in both the manufacturing and construction environment.
Make the Most Out of All Your Web Inquiries
Despite greater reliance on the internet for business, valued leads can be lost due to lack of follow-up. To help our own customers with this problem, Ciright announces the full integration of web inquiries. All the inquiries on the web are indexed as opportunities...
Ciright Commits to Medical Group System
Ciright announces the commitment of resources to Ciright Medical Group to continue development of what started in 1994 on the FAX RX and progresses through patient management and patient assessment to a fully HIPA compliant enterprise reporting system. This system...
Ciright Releases iPhone App
Ciright announces the availability of iRep, which is the iPhone application for integration for a mobile sales force back to an enterprises data. iRep stands for sales representative or manufacturer representative.

Recent Comments