
by Ciright | Jan 22, 2026 | Blogs
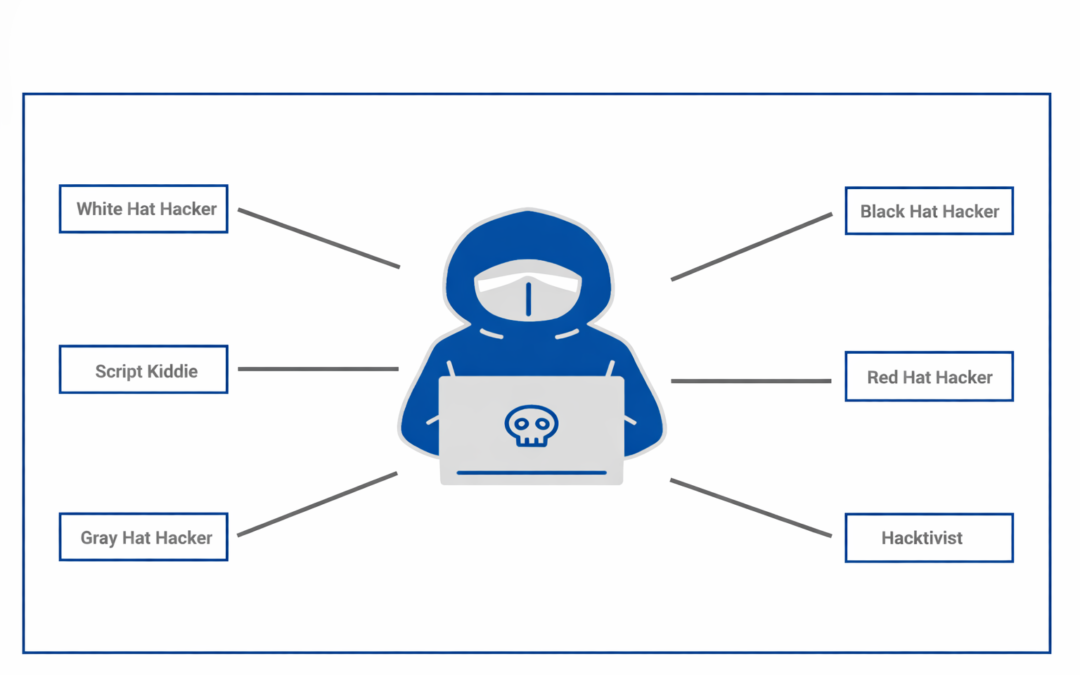
Dear Readers, As the world becomes increasingly reliant on technology, cybersecurity threats are becoming more prevalent. Hackers have evolved from the stereotypical image of a person sitting in a dark basement, typing away on a computer, to a diverse range of...

by Ciright | Jan 22, 2026 | Blogs
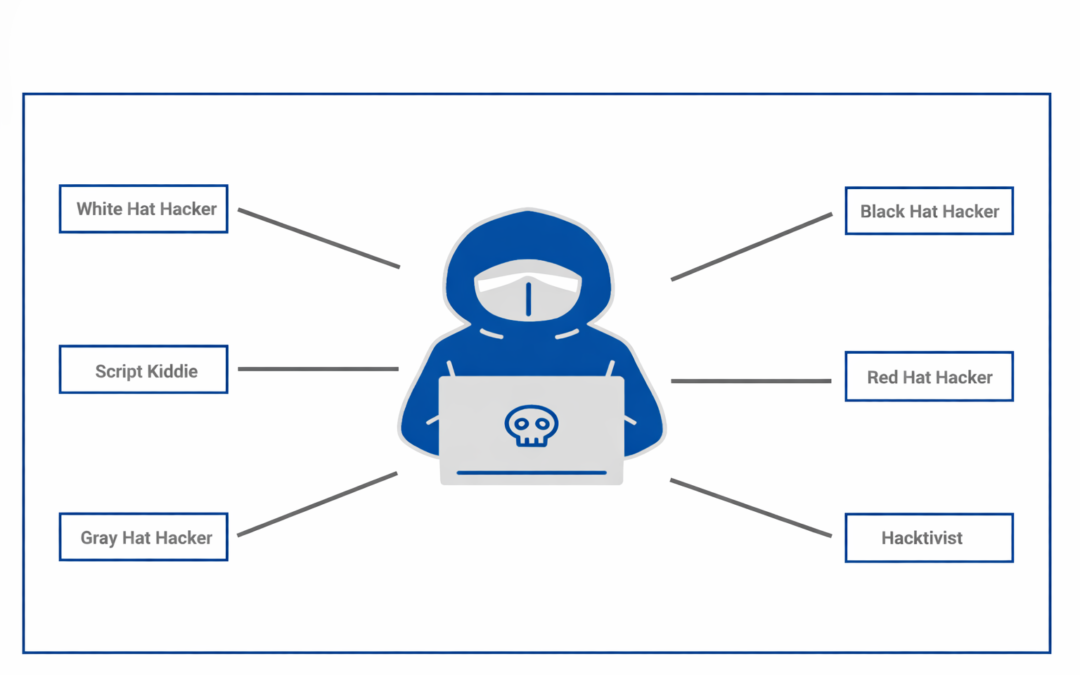
Dear Readers, This article has been written to provide a brief introduction to cardholder verification with EMV and the challenges posed by different verification methods. One objective of EMV was to drive down fraud; to do this we need to prove three things: The bank...

by Ciright | Jan 22, 2026 | Blogs
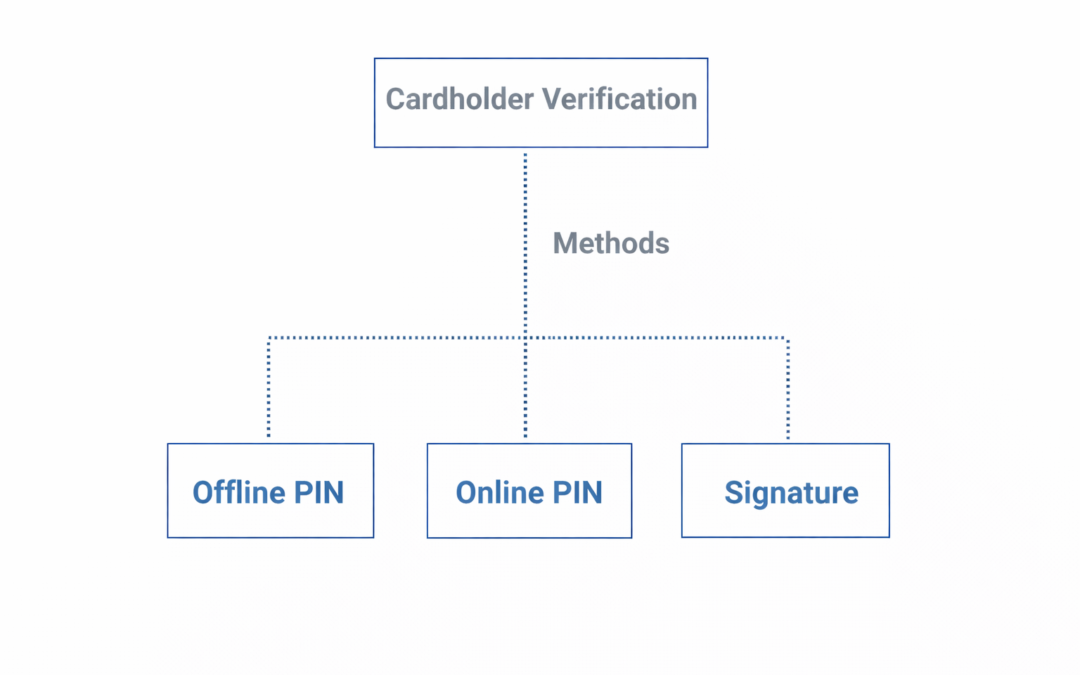
Dear Readers, In this blog we are going to learn about Card Action Analysis is a cutting-edge approach to understanding consumer behavior and market trends through the analysis of credit and debit card transactions. By dissecting spending patterns, purchase histories,...

by Ciright | Jan 22, 2026 | Blogs
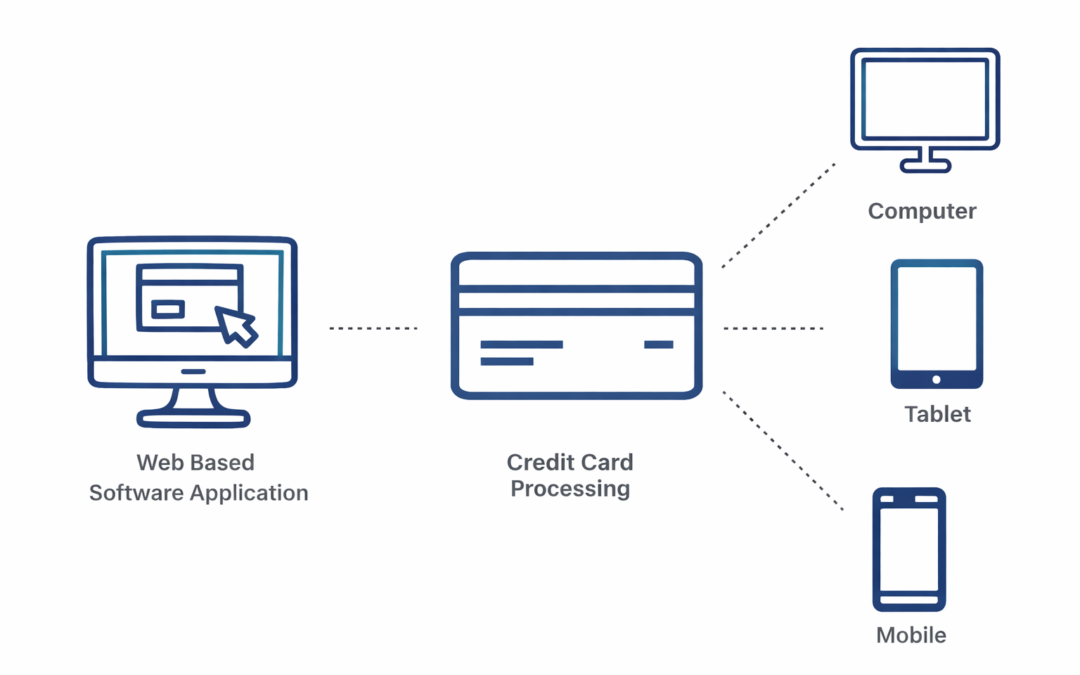
Dear Readers, In this blog we are going to learn about, A virtual terminal is a versatile web-based software application designed to streamline credit card processing for businesses, allowing them to accept card payments even when customers cannot physically present...

by Ciright | Jan 22, 2026 | Blogs
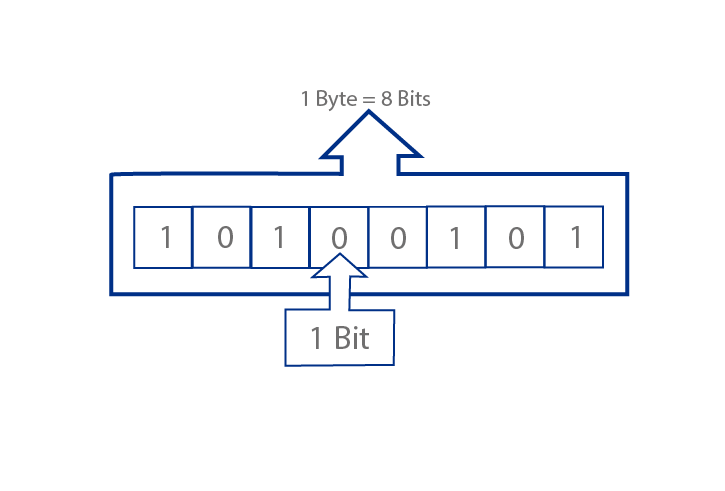
Dear Readers, At the smallest scale in the computer, information is stored as bits and bytes. In this section, we’ll learn how bits and bytes encode information. Bit a “bit” is atomic: the smallest unit of storage A bit stores just a 0 or 1 “In the computer it’s all...

Recent Comments