
by Ciright | Jan 23, 2026 | Blogs
Dear Readers, One of the nice things about chip cards (ICCs) is that the data that comes out of them is virtually always supplied in a standard format, called BER-TLV. In plain English: Basic Encoding Rules, Tag-Length-Value (a quaint but informative article about it...

by Ciright | Jan 23, 2026 | Blogs
Dear Readers, This week’s blog is about the Implementation, Best Practices, and Benefits of multi-factor authentication for organizations. Companies are developing or reinvigorating their cybersecurity risk management programs; it’s vital to remember that...

by Ciright | Jan 23, 2026 | Blogs
Dear Readers, Coverage Chart United States CanadaDrivers License Machine Readable Technologies for U.S. Jurisdictions (June2019) JurisdictionMagnetic Stripe2D BarcodeRadio FrequencyNotesAlabama YesYes Mag Added June...

by Ciright | Jan 23, 2026 | Blogs
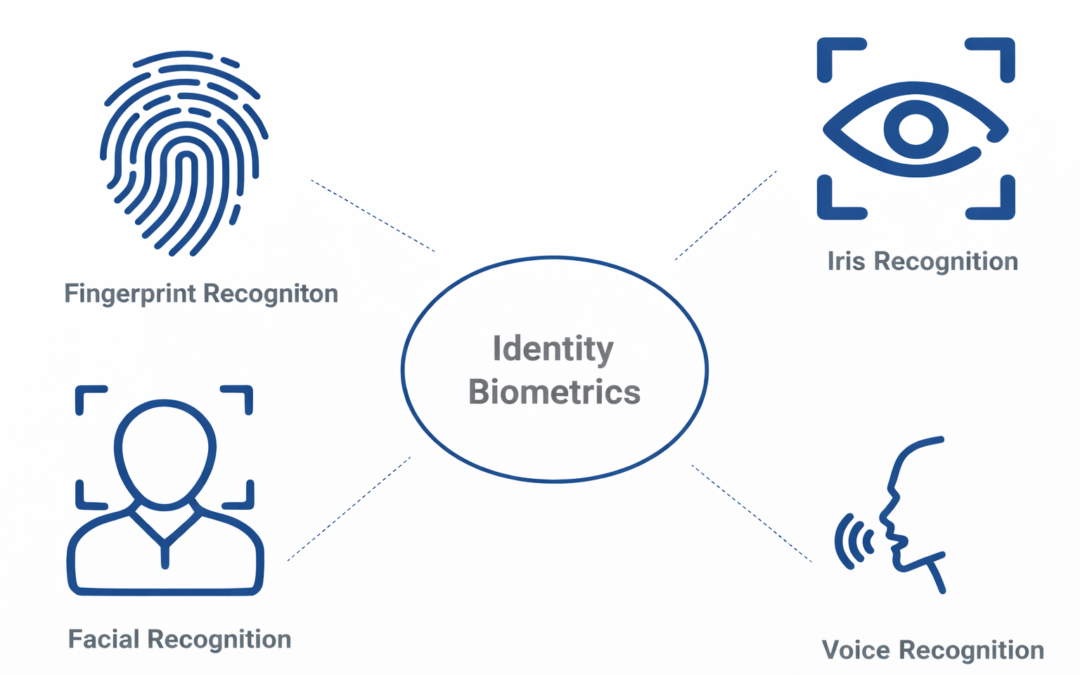
Dear Readers, For good cause, biometric authentication has grown in popularity as a means of identity verification. Biometric authentication, unlike traditional authentication methods such as passwords, relies on unique physical characteristics to verify an...

by Ciright | Jan 23, 2026 | Blogs
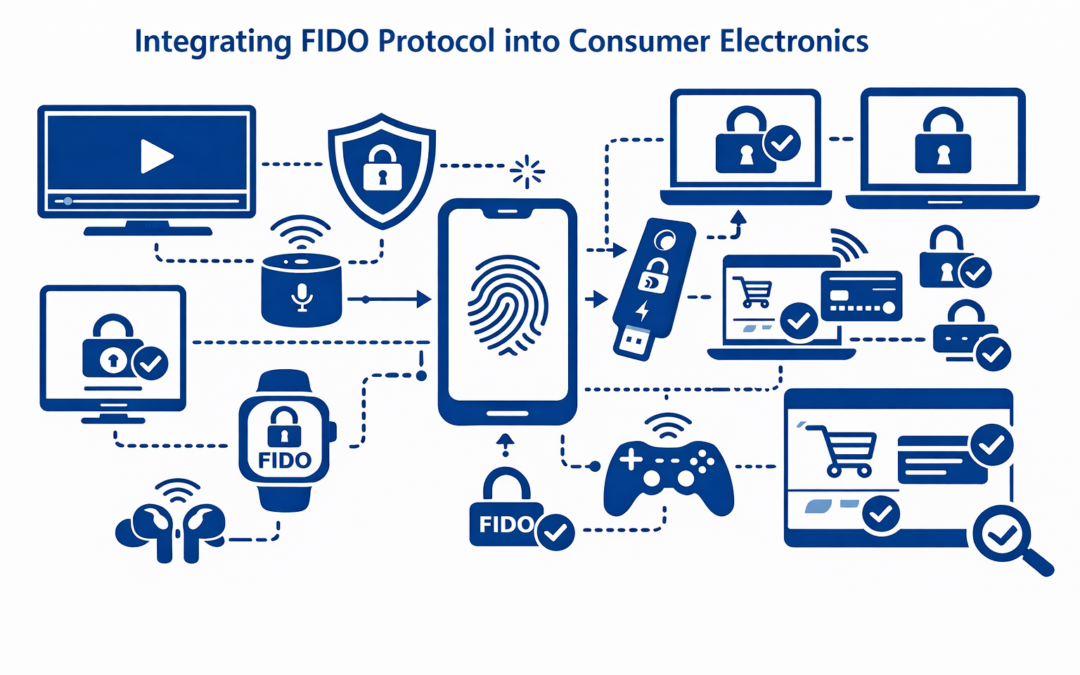
Executive Summary As cyber threats continue to grow in scale and sophistication, the need for stronger, phishing-resistant authentication mechanisms is more critical than ever. Ambimat Electronics, a leader in embedded hardware and secure microcontroller design,...



Recent Comments