![.jar [File Format]](data:image/gif;base64,R0lGODlhAQABAAAAACH5BAEKAAEALAAAAAABAAEAAAICTAEAOw==)
by Ciright | Jan 23, 2026 | Blogs
Dear Readers, A JAR (“Java archive”) file is a package file format typically used to aggregate many Java class files and associated metadata and resources (text, images, etc.) into one file for distribution.[4] JAR files are archive files that include a Java-specific...

by Ciright | Jan 23, 2026 | Blogs
Dear Readers, What is a public key? In cryptography, a public key is a large numerical value that is used to encrypt data. The key can be generated by a software program, but more often, it is provided by a trusted, designated authority and made available to...

by Ciright | Jan 23, 2026 | Blogs
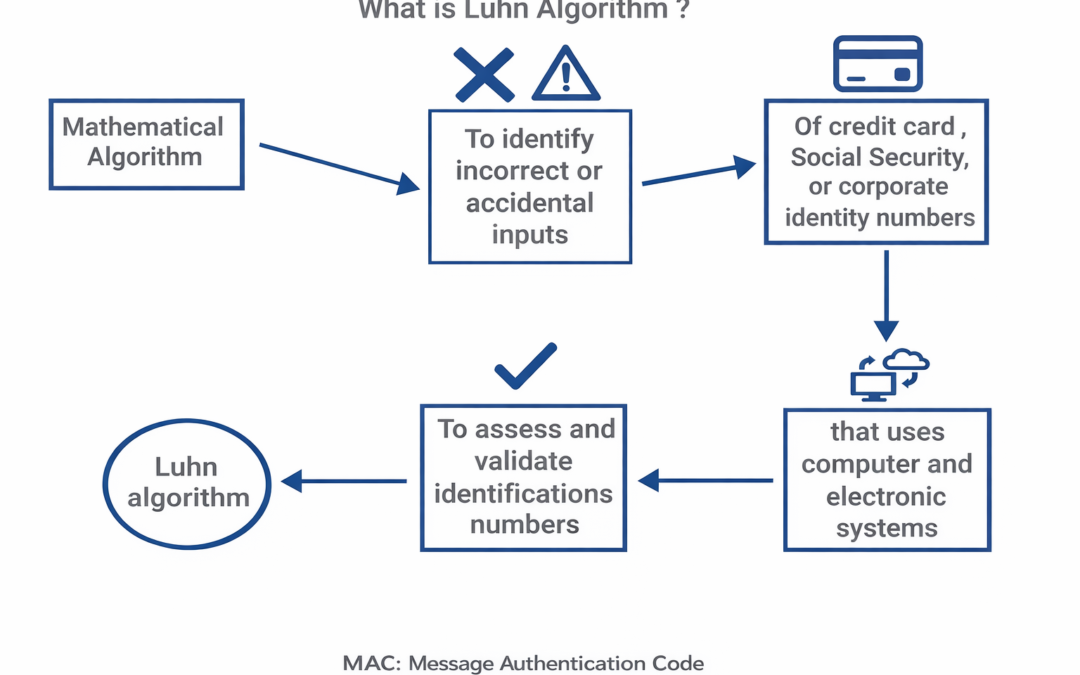
Dear Readers, The Luhn algorithm or Luhn formula, also known as the “modulus 10″ or “mod 10” algorithm, named after its creator, IBM scientist Hans Peter Luhn, is a simple checksum formula used to validate a variety of...

by Ciright | Jan 23, 2026 | Blogs
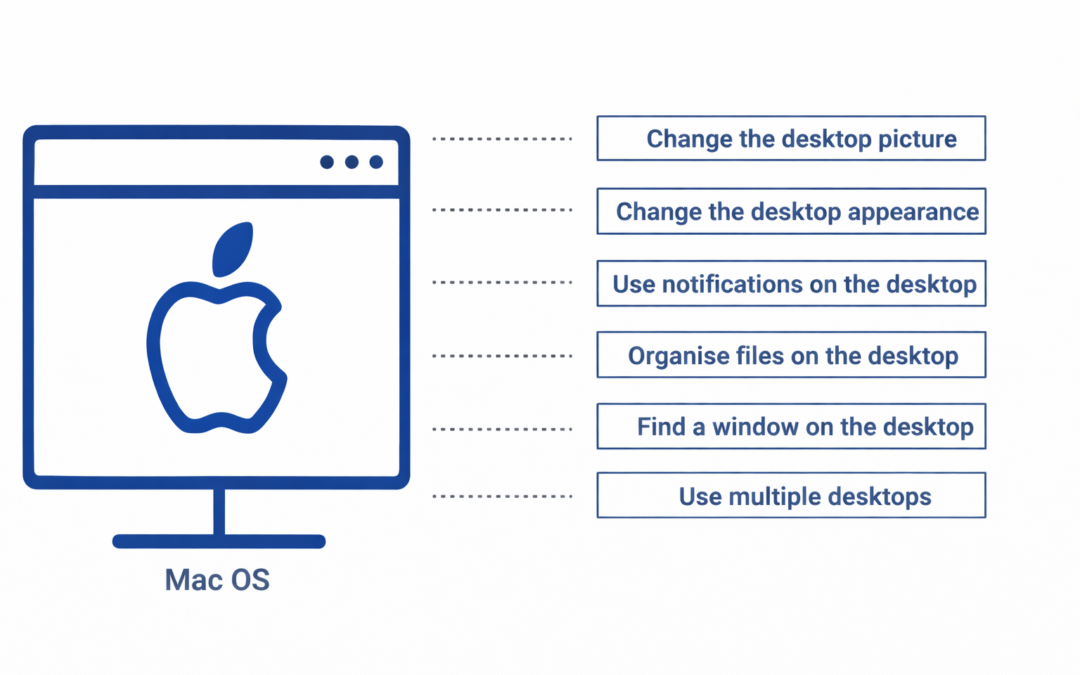
Dear Readers, Get to know the Mac desktop, At the top of the screen is the menu bar and at the bottom is the Dock. In between is what’s called the desktop. The desktop is where you do your work. Change the desktop picture You can choose a different...

by Ciright | Jan 23, 2026 | Blogs
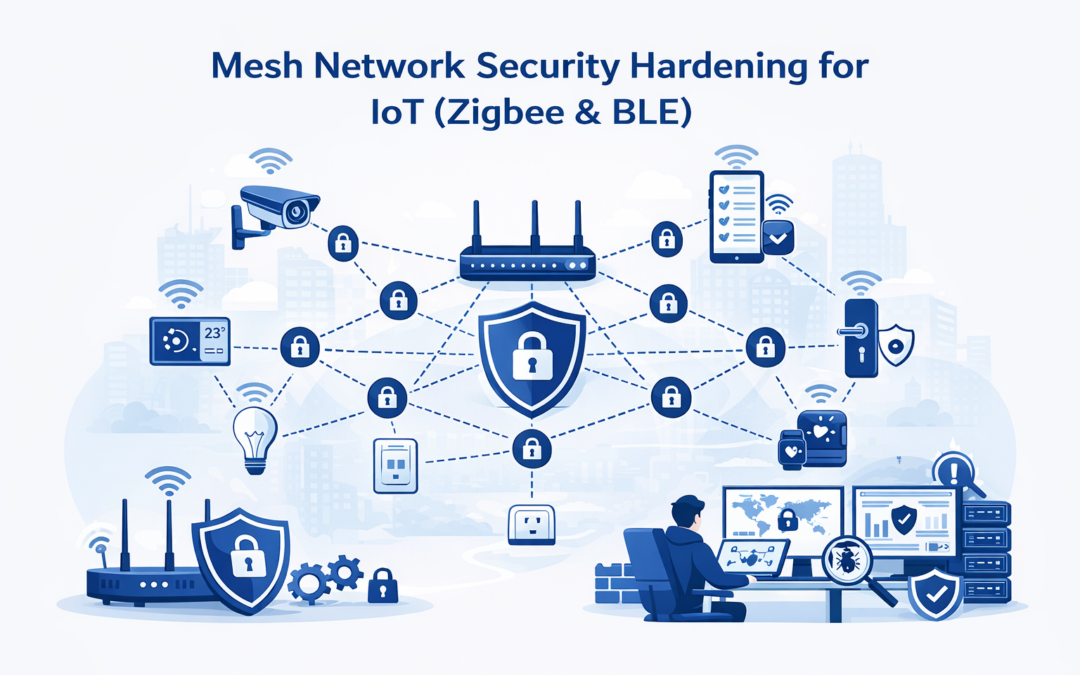
Executive Summary This white paper provides a detailed framework for hardening mesh network security in IoT deployments, with a focus on Zigbee 3.0 and Bluetooth Low Energy (BLE) Mesh. In smart city projects with thousands of devices, mesh networks...
![.jar [File Format]](https://ciright.com/wp-content/uploads/2026/01/jar-File-Format-1080x675.png)
![.jar [File Format]](https://ciright.com/wp-content/uploads/2026/01/jar-File-Format-1080x675.png)


Recent Comments